We learnt this week that the next Linux version (5.18) will add two important compilation warnings to avoid
potential security problems: -Warray-bounds and -Wzero-length-bounds. It’s a multi years effort, so it’s important to
celebrate.
Congratulations to the persons involved in these changes!
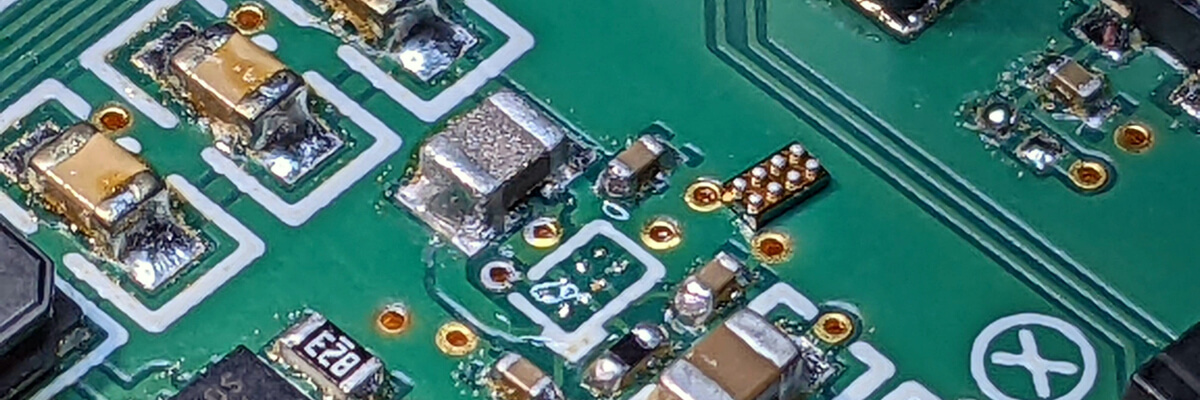
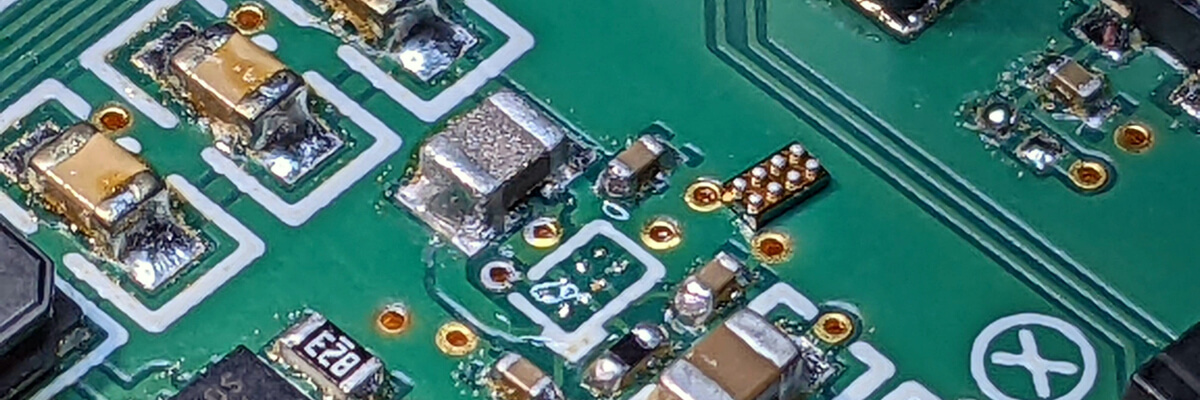
Thank you to Joseph Chiu for the header’s picture .
Happy reading!
Articles
Oxide on My Wrist: Hubris on PineTime was the best worst idea
For most of us (me included)
Hubris
is still a mysterious operating system
targeting microcontrollers. However it has few characteristics very interesting that might make you curious. Cliff, who works on Hubris,
describes them in
On Hubris And Humility
. Two of them that are the most interesting
from my point of view: First, drivers are outside the kernel and run in unprivileged mode. Second, Everything is defined at build time,
the tasks that could run but as well, the hardware resources available to them!
Assessing the Value of Coding Standards: An Empirical Study
An controversial study that tries to highlight the potential negative impacts to follow MISRA C rules too strictly.
The study focus on empirical evidences which I believe, it is the main reason why it is interesting to read.
Understanding Side Channel Attack Basics
A very nice introduction article on SCAs that walks us though a simple example to help us to understand the concept.
Voiding the warranty on a 1993 Minitel 2 to run arbitrary firmware
I believe you have to be over 30 to know what is the
Minitel
. In one sentence,
it is the World Wide Web before the World Wide Web through a unique custom terminal. Graphics were (very) limited, but
the hardware was capable of more than what the network could deliver. A good article to discover this big chunk of
the past.
Pulling Bits From ROM Silicon Die Images: Unknown Architecture
If the World of integrated circuit reverse engineering is calling you but you don’t know how too jump in, this
article can help yoo to dare. Ryan Cornateanu went through all the first stages and he describes them precisely
in this article.
Unwinding a Stack by Hand with Frame Pointers and ORC
A great article that makes us discover the details of the historic Linux
stack unwinder
that are the frame pointers and of ORC (Oops Replay Capability) the new system introduced in version 4.14.
Porting the Slint UI Toolkit to a Microcontroller with 264K RAM
That’s definitely one of the most impressive achievement I have read this year so far. It’s very interesting to discover how
Slint team managed to make a UI of this quality run on a such tiny target.
Tools
Depthcharge
So let’s say you are about to release or you already released a platform booting with U-Boot and you want to run some
analysis to find exploits or weaknesses? In these circumstances Depthcharge is the right tool to start with.
Check out this video to see what one can do with it
Sinking U-Boots with Depthcharge: Effective Exploitation of Boot-Time Security Debt
bcal - Byte CALculator
bcal is a very handy cli tool for those who love to work in a terminal and have to manipulate bits, bytes and addresses.
Misc
Running CP/M on the Raspberry Pi Pico microcontroller
A special misc for the fans of the
CP/M operating system
and/or of the
Z80 microprocessor
.
